**Introduction**
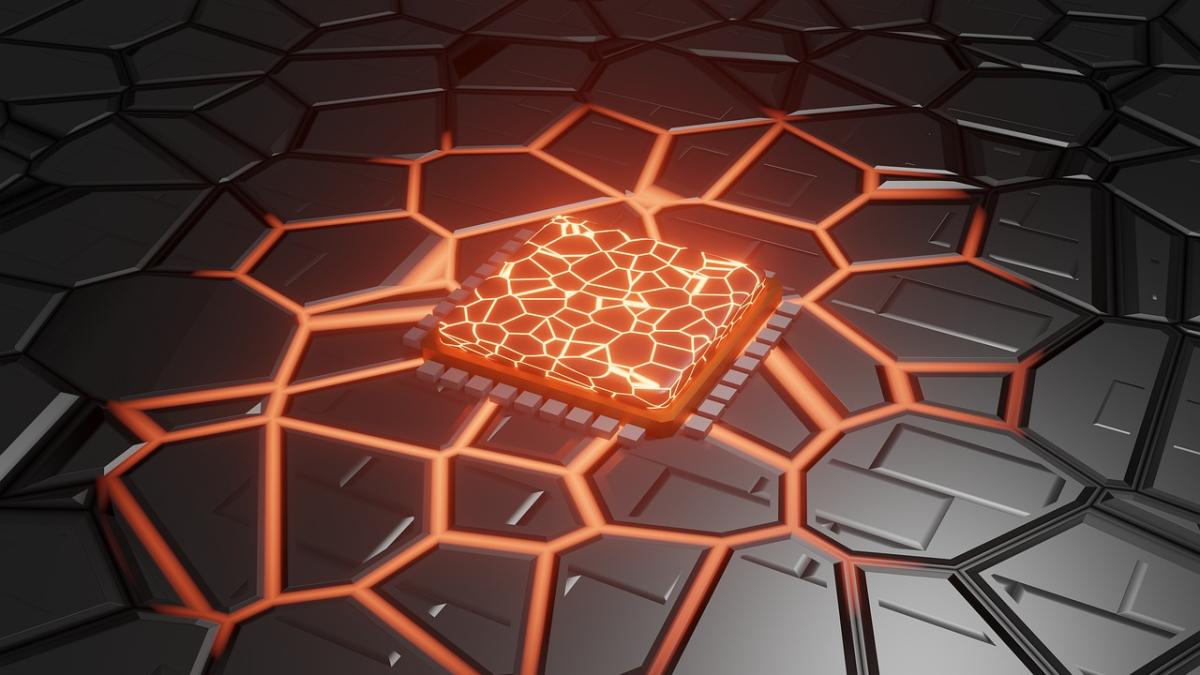
Robust hardware security is critical for protecting sensitive data in today’s digital ecosystem. Embedded security chips are evolving beyond traditional Trusted Platform Modules (TPMs) by integrating advanced encryption, biometric authentication, and blockchain‑based traceability directly into PC motherboards. This article explores the latest advancements in embedded security chips and how they reinforce system integrity and prevent unauthorized access.
**Technological Innovations**
- **Enhanced Cryptographic Engines:**
Embedded chips leverage next‑gen encryption algorithms and hardware security modules (HSMs) to protect firmware and data at every level.
- **Biometric Integration:**
Cutting‑edge sensors combine fingerprint, facial recognition, and even behavioral biometrics to continuously verify user identity.
- **Blockchain‑Backed Traceability:**
Distributed ledger technologies create immutable records of component histories, ensuring reliable tracking and authentication from manufacture to end‑user.
- **Real‑Time Anomaly Detection:**
AI‑driven monitoring systems continuously scan system behavior for signs of tampering or intrusion, triggering rapid countermeasures when security breaches are detected.
**Applications and Benefits**
- **Stronger Data Protection:**
Integrated security chips provide robust, hardware‑level safeguards that protect against firmware attacks and unauthorized access.
- **Enhanced Enterprise Compliance:**
These technologies help enterprises meet regulatory requirements, ensuring secure systems in finance, healthcare, and government sectors.
- **Continual User Authentication:**
Biometric and behavior-based verification ensure that access remains secure throughout device operation.
- **Improved System Trust:**
With an immutable, blockchain‑backed audit trail, users and businesses can trust the authenticity and integrity of their hardware.
**Future Directions**
Future enhancements may focus on integrating quantum‑resistant encryption algorithms and expanding biometric modalities to include iris and voice recognition. Deeper AI integration for continuous threat detection and automated response will further secure PC hardware against evolving cyber threats.
**Keywords:** embedded security chip, trusted computing, advanced TPM, hardware encryption, biometric security, blockchain traceability, secure PC, AI‑driven security, next‑gen cybersecurity
Embedded Security Chips
Chips for Trusted Computing: Beyond Traditional TPM
Related Articles
Unleash Your Power with High-Performance Gaming PCs
Get ready to elevate your gaming experience like never before
Unleash Power with High-Performance Gaming PCs
Elevate your gaming experience with unbeatable speed and graphics
Boost Your Game with High-Performance Gaming PCs
Power up your gaming experience and level up your skills
View our related products
See more